Rejuvenate IT News

From online transactions to cloud-based collaboration, digital tools have made it …Continue reading…

07 Aug
Built by Rejuvenate IT this client is obviously happy with their new website… Continue reading…
04 Aug
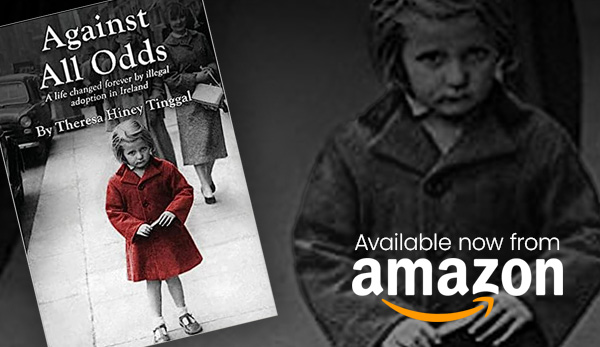
In a world where silence often drowns out the voices of injustice, there are individuals who choose to stand tall… Continue reading…

12 Apr
Rejuvenate IT would like to extend a big welcome to our latest team member, Christian… Continue reading…